Accudemia: How do I enable SAML SSO (Single Sign-On) for my account?

For the Updated Version of Accudemia 7.0 Click the link below:
This new feature to authenticate users using the SAML protocols for SSO to simplify passwords management and increase security that will allow your students to login to Accudemia from your college portal rather than a separate webpage/URL should be relatively easy to setup in Accudemia. And here's how:
Configuring Accudemia
- Login to your school's https://<mycollege>.accudemia.net website using your domain in place of the <mycollege> and admin credentials provided.
- Now to enable this option, you can access the setup under the Administration > Control Panel > User Accounts section form the left-side navigation menu.
- In the User Accounts page of your Accudemia website scroll down to the SAML Single Sign-On section.
- Here you'll enable SSO by checking the checkbox labeled "Enable SAML SSO".
- You'll now need to set the Identity Provider URL, Public Certificate, and Logout URL to Accudemia so it knows where the Users will be coming from and directed after they logout. Optionally there are other things you can do if needed too such as error page and alternate ID use (if uploaded into Accudemia specifically for SSO). Here is an sample of this completed:
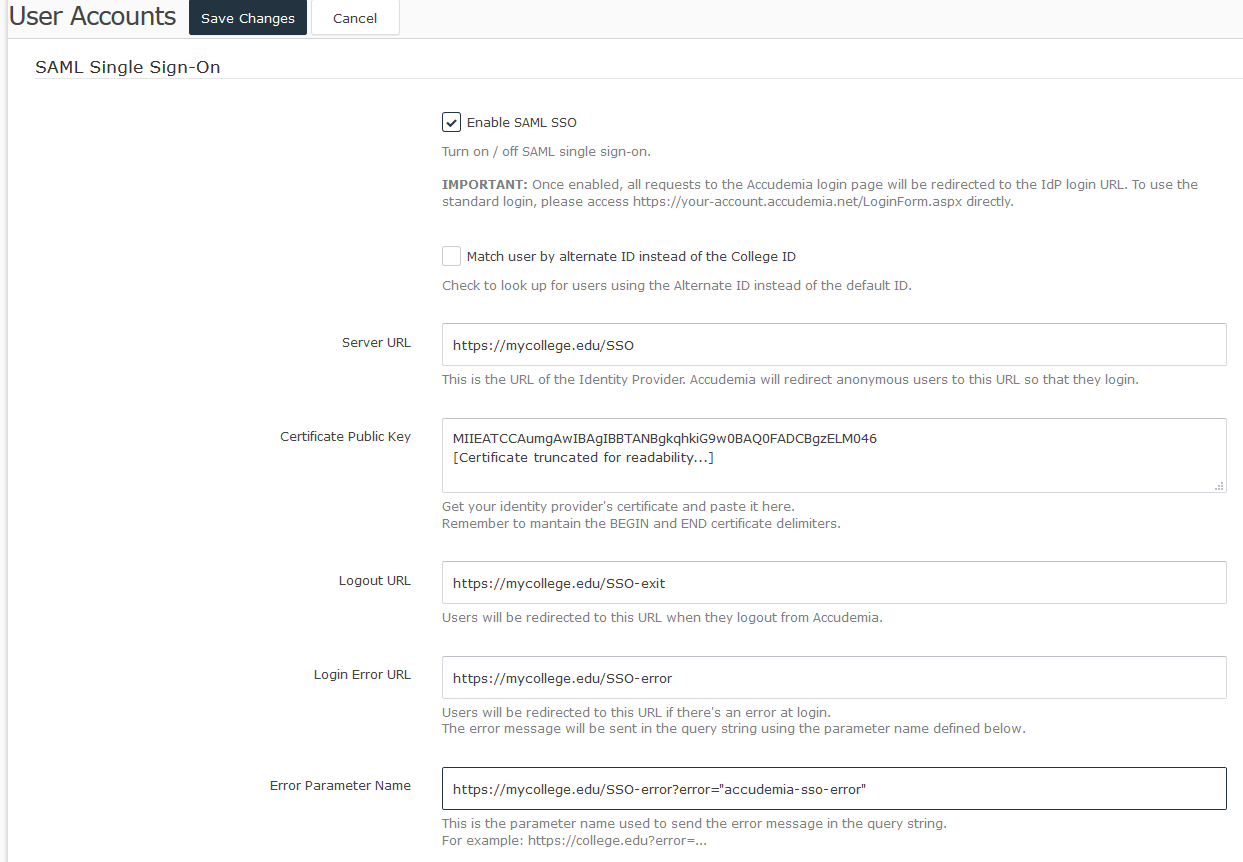
- Once done completing this section please be sure to save this information at the top of the page by clicking on the Save Changes button.
- Done! Now to test it go to your portal that you have setup for users and attempt to login using your credentials or a test user account.
Configuring your IdP / SAML Server
To configure your Identity Provider (IdP), you need the Accudemia SAML Metadata. You can find it in:
https://<your-domain>.accudemia.net/saml/metadata.aspx
Once you have entered the metadata in your IdP, you will need to set it up to send the user ID or alternate ID in the NameID field, under the Subject tag. It's important to note that the NameID doesn't have to an attribute, but the tag that's defined under the Subject node/tag in the XML. If you look at the SAML authentication request, it should look like this:
- <saml:Subject>
- <saml:NameID Format="urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified">111-11-1111</saml:NameID>
- ...
- </saml:Subject>
Configuring Active Directory Federation Services (ADFS)
In order to send the NameID in the Subject tag, you need to go to AD FS Management, navigate to Trust Relationships > Claims Provider Trusts, then right-click on your provider and select Edit Claim Rules:
Then click Add Rule and add the following rules:
First, to send the LDAP attribute as a claim, create a rule of type "Send LDAP Attributes as Claims". Set the attribute you want to use to authenticate from your AD. For example, the Employee Number:
Then, create a second rule. This time, select "Transform an Incoming Claim". in another rule transform the NameID to the Subject:
For more information you can also checkout this video:
For any questions regarding this new feature, please contact our support team at support@accudemia.com or simply Submit a Ticket on this site.
Related Articles
AccuCampus: How to set up SAML SSO authentication?
Introduction This feature authenticates users using the SAML protocols for SSO. It simplifies password management, increases security, and allows students to log into AccuCampus from a unique college portal, rather than a separate webpage/URL. This ...Accudemia: How do I bypass SSO to log in directly?
Introduction Accudemia can be set up to utilize a Single-Sign-On (SSO) system using Security Authentication Markup Language (SAML). This is a tool that allows users to only require one set of login information across an entire system. SSO will ...Accudemia: How do I enable SAML SSO (Single Sign-On) for my account?
Introduction This feature authenticates users using the SAML protocols for SSO. It simplifies password management, increases security, and allows students to log into Accudemia from a unique college portal, rather than a separate webpage/URL. This ...Single Sign-On Requirements for AccuCampus
Introduction The aim of this document is to explain how to integrate your own site or portal with AccuCampus. It also includes usage examples so you can get started faster. This alternative access method would allow you to integrate AccuCampus into ...Accudemia: How can I sign into the Accudemia app through Single Sign-On?
Introduction In this guide, we'll explain how you can login to the Accudemia app without using a username or password for Accudemia, but instead using your SSO credentials. Please note that this requires a logging through a browser on another device ...